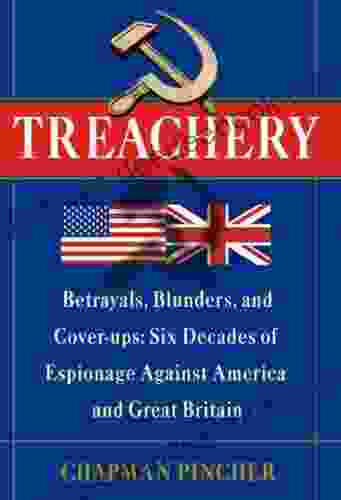
Six Decades of Espionage Against America and Great Britain: A Comprehensive Investigation

Espionage, the act of spying and gathering secret information, has been a constant threat to nations throughout history. In the modern era, espionage has evolved into a complex and sophisticated game, with spies employing cutting-edge technology and engaging in elaborate plots to compromise national security.
4.4 out of 5
| Language | : | English |
| File size | : | 1641 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 704 pages |
| Paperback | : | 52 pages |
| Item Weight | : | 5.9 ounces |
| Dimensions | : | 8 x 0.13 x 10 inches |
For over six decades, a network of spies has been operating against America and Great Britain, conducting covert operations with devastating consequences. These spies have infiltrated government agencies, stolen sensitive secrets, and compromised critical infrastructure, all in the pursuit of power and influence.
This article will delve into the intricate world of espionage against America and Great Britain, exploring the motivations, methods, and consequences of this clandestine activity. We will examine the key players involved, the techniques they employ, and the impact their actions have had on the security and well-being of these nations.
The Players Involved
The espionage network operating against America and Great Britain is composed of a diverse group of individuals and organizations, each with their own motivations and objectives. These include:
- Foreign intelligence agencies: State-sponsored intelligence agencies from countries such as Russia, China, and Iran are the primary perpetrators of espionage against America and Great Britain. These agencies are tasked with collecting intelligence on behalf of their governments, often through covert operations and espionage.
- Cybercriminals: In recent years, cybercriminals have become increasingly involved in espionage, using their technical skills to hack into computer systems and steal sensitive data. Cybercriminals may be motivated by financial gain, political activism, or simply the challenge of hacking into secure systems.
- Terrorist organizations: Terrorist organizations also engage in espionage to gather intelligence on potential targets and plan attacks. Terrorists may use spies to infiltrate law enforcement agencies, monitor communications, or gather information on critical infrastructure.
- Disgruntled employees and contractors: In some cases, espionage is committed by disgruntled employees or contractors who have access to sensitive information. These individuals may be motivated by personal grievances, financial gain, or a desire to harm their former employers.
Methods of Espionage
Espionage is conducted through a variety of methods, including:
- Human intelligence (HUMINT): HUMINT involves the use of human agents to gather intelligence. Spies may be recruited from within target organizations, or they may be planted in key positions to gain access to sensitive information. HUMINT is a highly effective method of espionage, as it allows spies to gather information that is not available through other means.
- Signals intelligence (SIGINT): SIGINT involves the interception and analysis of electronic communications, such as phone calls, emails, and text messages. SIGINT can be used to gather a wide range of intelligence, including military secrets, diplomatic communications, and financial information.
- Cyber espionage: Cyber espionage involves the use of computers and the internet to steal sensitive data from target systems. Cyber spies may use malware, phishing attacks, or other techniques to gain access to computer networks and steal information.
- Physical surveillance: Physical surveillance involves the跟踪 and observation of individuals or organizations. Spies may use cameras, binoculars, and other equipment to gather information on their targets.
Consequences of Espionage
Espionage can have devastating consequences for America and Great Britain. The theft of sensitive information can compromise national security, threaten economic stability, and undermine trust between allies. Espionage can also lead to the loss of life, as spies may gather intelligence on military operations or terrorist plots.
In recent years, espionage has become increasingly sophisticated, with spies using advanced technology to steal information and evade detection. This has made it more difficult for America and Great Britain to protect their secrets and ensure their national security.
Espionage is a serious threat to America and Great Britain, and it is a threat that is constantly evolving. The spies who operate against these nations are highly skilled and determined, and they are constantly seeking new ways to compromise their security.
America and Great Britain must remain vigilant in their efforts to counter espionage. They must invest in new technologies and strategies to detect and disrupt espionage operations. They must also work together with allies to share intelligence and coordinate their efforts.
The battle against espionage is a never-ending one, but it is a battle that America and Great Britain must win. The security of these nations depends on it.
4.4 out of 5
| Language | : | English |
| File size | : | 1641 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 704 pages |
| Paperback | : | 52 pages |
| Item Weight | : | 5.9 ounces |
| Dimensions | : | 8 x 0.13 x 10 inches |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Bibliography
Bibliography Preface
Preface Synopsis
Synopsis Annotation
Annotation Manuscript
Manuscript Tome
Tome Classics
Classics Narrative
Narrative Biography
Biography Memoir
Memoir Dictionary
Dictionary Character
Character Librarian
Librarian Catalog
Catalog Card Catalog
Card Catalog Archives
Archives Study
Study Research
Research Lending
Lending Reserve
Reserve Academic
Academic Rare Books
Rare Books Special Collections
Special Collections Interlibrary
Interlibrary Literacy
Literacy Awards
Awards Reading List
Reading List Book Club
Book Club Kana Tucker
Kana Tucker Adrian Harte
Adrian Harte Karen An Hwei Lee
Karen An Hwei Lee Manoj Joshi
Manoj Joshi Lakshmi Menon
Lakshmi Menon Nina Mjagkij
Nina Mjagkij John W Pearson
John W Pearson George Amberg
George Amberg Rob Larson
Rob Larson Naomi Wolf
Naomi Wolf Katherine C Zubko
Katherine C Zubko David Frykman
David Frykman Stephen Miller
Stephen Miller Wendy Wax
Wendy Wax Serge Marquis
Serge Marquis Martin R Howard
Martin R Howard Lori Sue Roach
Lori Sue Roach Christopher Paslay
Christopher Paslay Olivier Dard
Olivier Dard Elisa Chavarri
Elisa Chavarri
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 William WordsworthThe Area Manager Diary 1987 To 1988 Volume: A Nostalgic Journey into the Past
William WordsworthThe Area Manager Diary 1987 To 1988 Volume: A Nostalgic Journey into the Past
 Chance FosterThe Coming Novel Daniel Black: A Thrilling Tale of Espionage, Betrayal, and...
Chance FosterThe Coming Novel Daniel Black: A Thrilling Tale of Espionage, Betrayal, and... Ralph TurnerFollow ·11.7k
Ralph TurnerFollow ·11.7k Jason HayesFollow ·15.5k
Jason HayesFollow ·15.5k Deion SimmonsFollow ·10.3k
Deion SimmonsFollow ·10.3k E.M. ForsterFollow ·16.9k
E.M. ForsterFollow ·16.9k Jackson BlairFollow ·12.7k
Jackson BlairFollow ·12.7k Marcus BellFollow ·3.9k
Marcus BellFollow ·3.9k Chuck MitchellFollow ·18.5k
Chuck MitchellFollow ·18.5k Oscar BellFollow ·3.7k
Oscar BellFollow ·3.7k
 Willie Blair
Willie BlairLords of the White Castle: A Comprehensive Analysis of...
In the realm of...
 Dwight Bell
Dwight BellFixed Effects Regression Models: Quantitative...
Fixed effects...
 Ivan Turner
Ivan TurnerHomes Around the World: A Journey Through Architectural...
Our homes are more than...

 Miguel de Cervantes
Miguel de CervantesThe Essentials For Standards Driven Classrooms: A...
In today's educational landscape, the...
 Colton Carter
Colton CarterEugenics, Social Reform, and the Legacy of...
The early 20th century marked a period...
4.4 out of 5
| Language | : | English |
| File size | : | 1641 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 704 pages |
| Paperback | : | 52 pages |
| Item Weight | : | 5.9 ounces |
| Dimensions | : | 8 x 0.13 x 10 inches |